What is SSO? How It Works & Key Benefits Explained
April 28, 2026
By
Evie Secilmis

When you think about strengthening your company’s security, you probably think about adding more complexity, like longer passwords or stricter rules. But what if one of the most effective security tools actually made life simpler for your team? That’s the core idea behind Single Sign-On (SSO). By centralizing authentication, you encourage the use of one single, strong password instead of many weak, recycled ones. This simple shift dramatically reduces your vulnerability to common cyber threats. So, what is a SSO and how does this one change improve security? It’s a system that provides a single, secure gateway to all your applications, making it easier to protect your sensitive sales data.
Key Takeaways
- SSO is a win for both efficiency and security: It gives your team one password for all their tools, which reduces login friction and encourages everyone to use a single, stronger password instead of juggling multiple weak ones.
- Combine SSO with MFA for the best protection: Think of SSO as the convenient master key and Multi-Factor Authentication (MFA) as the essential security code. Using them together provides a streamlined login experience for your team while adding a powerful defense against unauthorized access.
- A successful rollout requires a clear plan: Before you begin, confirm that your SSO solution works with your team's essential software. A smooth transition depends on having a strategy that includes setting clear security policies and training your team on the new workflow.
What is Single Sign-On (SSO)?
Think of Single Sign-On (SSO) as a master key for your digital world. Instead of fumbling for a different key for every door, like your email, your CRM, or your project management tool, you use one single, secure key to open them all. In technical terms, SSO is an authentication process that allows you to access multiple applications and services using just one set of login credentials. Once you sign in to one tool, you’re automatically signed in to all the others connected through your company’s SSO system. For busy sales teams, this means you can move seamlessly between drafting a proposal in Iris and updating a client’s status in your CRM without repeatedly typing in passwords. It’s a simple concept that removes a surprising amount of daily friction.
Why SSO Matters
At first glance, SSO might seem like a simple convenience, but its impact is much bigger. For starters, it significantly strengthens security. When your team members only have to remember one password, they’re more likely to make it a strong, complex one. This reduces the risk of using weak or repeated passwords across different platforms, which is a common entry point for security breaches. It’s a straightforward way to improve security hygiene without adding complexity for your team.
Beyond security, SSO saves valuable time and reduces frustration. Think about how much time is lost to forgotten passwords and reset requests. By eliminating this recurring issue, your team stays productive and focused. This also lightens the load on your IT department, freeing them from a constant stream of password-related support tickets so they can work on more strategic projects.
SSO vs. Traditional Logins
The difference between using SSO and traditional logins is like the difference between an all-access pass and a pocketful of individual tickets. With traditional logins, you have to present a separate ticket for every single application you use. You enter your username and password for your email, then do it all over again for your sales software, and again for your team chat. This constant need to re-authenticate leads to what’s known as "password fatigue."
This fatigue often causes people to resort to insecure habits, like writing passwords on sticky notes or using the same simple password everywhere. SSO solves this problem entirely. You log in once at the start of your day, and the system handles the authentication for all other connected apps behind the scenes. It’s a true single sign-on experience that provides secure, uninterrupted access to your tools.
How Does SSO Work?
At first glance, Single Sign-On might seem like a bit of digital magic. You log in to one application, and suddenly you have access to all your other work tools without typing another password. But the process behind it is actually quite logical. It all comes down to a secure, trust-based relationship between your applications and a central authentication service. Let's break down the steps and the key players involved.
The Authentication Process Explained
Think of SSO as having a master keycard for your office building. Instead of needing a separate key for every single room (your email, your CRM, your proposal software), you use one card to get into the main door. Once you're in, the building's security system recognizes your card and grants you access to all the rooms you're authorized to enter. SSO works the same way for your digital workspace. You enter your credentials just once, and this single act of authentication confirms your identity for all connected applications, saving you time and the headache of remembering multiple passwords.
Key Players: Identity Providers and Service Providers
The SSO process relies on two main parties working together: the Identity Provider (IdP) and the Service Provider (SP). The Service Provider is the application or website you want to access, like your company’s project management tool or sales database. The Identity Provider is the system that manages your digital identity and credentials; think of well-known IdPs like Google, Microsoft, or Okta. When you try to log in to an SP, it redirects you to your IdP to verify who you are. Essentially, the SP trusts the IdP to handle the security check, creating a seamless digital handshake between the two systems.
How Tokens and Sessions Keep You Logged In
So, how do you stay logged in as you move between different apps? The secret is a small piece of data called an authentication token. After you successfully log in through your Identity Provider, it generates a secure, encrypted token and sends it to your web browser. This token acts like a temporary digital passport. When you open another connected application, that Service Provider sees the token from your browser. It then verifies the token with the Identity Provider to confirm your identity without you having to do a thing. This all happens instantly in the background, creating a continuous session that lets you work smoothly across your tools. This system of SSO tokens is what makes the whole process possible.
What Are the Benefits of SSO?
So, why should your team care about SSO? Beyond the tech jargon, single sign-on offers some very real, tangible benefits that make daily work smoother, safer, and more efficient. Think of it as a universal key for all your digital tools. Instead of fumbling with a giant keychain of different passwords for your CRM, your proposal software, and your communication apps, your team gets one secure key to open every door.
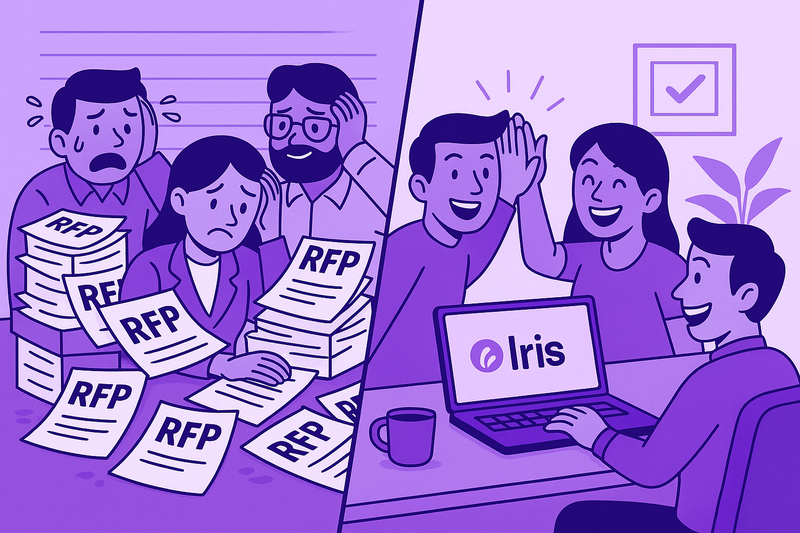
This isn't just about convenience. Implementing SSO is a strategic move that streamlines workflows, strengthens your company's security posture, and frees up your IT team from the endless cycle of password-related support tickets. It allows everyone to focus on what they do best, whether that's closing deals or supporting the tech that makes it all happen. For a sales team using a suite of tools like the Iris platform, this means less time logging in and more time responding to RFPs and winning deals. The core idea is to remove friction. Every minute your team spends trying to remember a password or waiting for a reset link is a minute they aren't selling. By centralizing authentication, SSO gives that time back, creating a more focused and effective work environment for everyone involved.
A Better Experience for Your Team
Let's be honest, your sales team has better things to do than remember a dozen different passwords. SSO creates a much smoother workflow by connecting all their essential tools, from cloud apps to internal systems, under a single login. When your team can access their entire tech stack without friction, they spend less time on frustrating login screens and more time focusing on their actual work. This seamless experience directly contributes to increased productivity, helping your team stay in the zone and move deals forward without unnecessary interruptions. It’s a simple change that makes a big difference in their day-to-day efficiency.
Stronger, Simpler Security
One of the biggest wins with SSO is the major improvement to your security. It might sound backward, but having one password can be much safer than having many. Why? Because it encourages everyone to create and remember one truly strong, complex password instead of recycling simple, weak ones across multiple platforms. This simple shift dramatically reduces your vulnerability to common cyber attacks like phishing and credential stuffing. Plus, security management becomes centralized. You can enforce strong password policies and, when an employee leaves, you can revoke their access to every single application in one click, sealing potential security gaps instantly.
Less Administrative Work for IT
Your IT team will thank you for implementing SSO. It significantly cuts down on their administrative workload, especially the constant stream of password reset requests. By simplifying the login process, you free up your IT specialists to focus on high-impact projects that drive growth instead of handling repetitive support tickets. Onboarding new team members is also faster, as you can grant them access to all their necessary tools from a single dashboard. This boost in operational efficiency means your entire organization can move faster and more securely, letting your sales team sell and your tech team innovate.
Understanding the Risks and Challenges of SSO
While SSO is a fantastic tool for convenience and security, it’s not without its own set of challenges. It’s important to go in with your eyes open and understand the potential downsides. Being aware of these risks helps you put the right safeguards in place from the start, so you can get all the benefits of SSO without the potential headaches. Thinking through these challenges ensures your implementation goes smoothly and keeps your company’s data secure.
The "Single Point of Failure" Problem
The biggest risk with SSO is that it creates a single point of failure. Think of it like a master key for your office; if it goes missing, no one can get in. Similarly, if your SSO provider has an outage, your team could be locked out of all the applications they need to do their jobs. This is why having a solid disaster recovery plan is non-negotiable. You need a clear backup process for how your team can access critical systems if your SSO service is temporarily unavailable.
The Impact of a Compromised Account
Just as SSO provides a single point of entry, it also creates a single target for attackers. If a hacker steals an employee's SSO credentials, they don't just get one account; they get the "keys to the kingdom." This one password could give them access to your CRM, project management tools, and financial software. It dramatically raises the stakes for account security. To counter this risk, it's essential to pair SSO with multi-factor authentication (MFA). This requires a second form of verification, making it much harder for an unauthorized person to gain access.
Privacy and Data Sharing Concerns
When you use an SSO service, you're trusting it to manage how your data is shared between applications. Early versions of SSO didn't give users much say over what personal information was passed to a new website, creating privacy issues. Thankfully, modern SSO protocols have largely solved this by giving users and administrators more control over data sharing. With privacy regulations like GDPR becoming standard, it's crucial to choose an SSO solution that prioritizes user consent and transparently manages how personal information is used across different platforms.
SSO vs. Multi-Factor Authentication (MFA)
It’s easy to get Single Sign-On (SSO) and Multi-Factor Authentication (MFA) mixed up, since they both deal with how you log into your accounts. Think of them not as competitors, but as two different tools that work together to make your digital life both easier and safer. SSO is all about convenience and simplifying access, while MFA is focused on adding layers of security to verify you are who you say you are.
One simplifies your first step through the door, and the other makes sure that door is properly locked behind you. Understanding how each one works helps you see why using both is the best approach for protecting your company’s sensitive information, whether it's in your CRM or a proposal tool like Iris.
What's the Difference?
Let's break it down simply. Single Sign-On (SSO) is a tool that lets you log in once with a single username and password to access many different applications. Instead of juggling dozens of passwords for all your work apps, you just have one. It’s like having a single master key that opens all the doors in your office building.
Multi-Factor Authentication (MFA), on the other hand, is an extra security check. It requires you to provide more than one piece of evidence to prove your identity. This usually involves something you know (like your password) plus something you have (like a code sent to your phone) or something you are (like a fingerprint). It’s the digital equivalent of needing your key and a special security code to get past the front desk.
Why They're Better Together
This isn't an either-or situation; SSO and MFA are a perfect pair. SSO gives your team the convenience of a single, streamlined login process, which cuts down on password fatigue and forgotten credentials. But that convenience also creates a single point of entry, which needs to be protected. That’s where MFA comes in.
By adding MFA to your SSO system, you get the best of both worlds. Your team enjoys easy access to all their tools, while you ensure that access is secure. This combination significantly reduces the risk of unauthorized access, because even if a hacker steals your team member’s password, they won’t be able to get in without that second verification factor. It’s a simple way to add a powerful layer of defense.
A Quick Guide to SSO Protocols
Single Sign-On doesn't just happen by magic. It relies on a set of rules and standards called protocols to work securely. Think of these protocols as the languages that different applications and identity providers use to talk to each other. While you don't need to be a developer to understand the basics, knowing the key players can help you appreciate what’s happening behind the scenes. The three most common protocols you'll encounter are SAML, OAuth with OpenID Connect, and LDAP. Each one handles authentication a bit differently, but they all share the same goal: to make access simple and secure.
SAML
SAML, which stands for Security Assertion Markup Language, is a well-established protocol for exchanging authentication and authorization information. It’s a popular choice for enterprise environments. Here’s the gist: when you try to log into an application (the service provider), it redirects you to your company’s identity provider. Once you’re verified, the identity provider sends a digitally signed SAML assertion back to the application, confirming who you are and what you can access. It’s like a digital hall pass that proves you’re allowed in without you having to show your ID at every door.
OAuth and OpenID Connect
You’ve probably used OAuth and OpenID Connect without even realizing it, especially if you’ve ever used a "Log in with Google" button. OAuth (Open Authorization) is a protocol that lets one application access your data in another application on your behalf, without you sharing your password. Think of it as giving an app permission to do something specific. OpenID Connect is a thin layer that sits on top of OAuth 2.0 to add an identity component. While OAuth is about authorization (what you can do), OpenID Connect is about authentication (who you are), making the combination perfect for modern web and mobile applications.
LDAP
LDAP, or Lightweight Directory Access Protocol, is a bit different from the others. It’s a protocol for accessing and managing information in a directory, which is essentially a specialized database that stores user information like names, passwords, and permissions. Many organizations use an LDAP directory as a central source of truth for user identities. While it can be used for authentication in an SSO system, it’s often the underlying directory that other protocols like SAML connect with to verify a user’s credentials. It’s a foundational piece of many corporate IT infrastructures for managing user access.
Before You Implement SSO: Key Considerations
Jumping into SSO can transform how your team works, but a little prep work is key to a smooth transition. Before you flip the switch, it’s important to think through a few things to make sure the rollout is successful. Taking the time to plan now will save you headaches later and ensure you get the most out of your new system. From security to software, here’s what to consider.
Assess Your Security Requirements
One of the biggest draws of SSO is how it can improve your security posture. By giving your team one secure way to log in, you can dramatically reduce the risk of password fatigue and the weak password habits that come with it. But before you can get there, you need to be clear on your specific security needs. Think about your organization’s structure. Does your sales team need the same level of access as your engineering team? Are there specific compliance standards you need to meet? Answering these questions will help you choose an SSO provider that fits your requirements and configure it correctly from day one.
Check for System Compatibility
Your SSO solution will act as the central gateway to all the other apps your team relies on, so it needs to connect seamlessly. A successful implementation depends on compatibility with existing systems, from your CRM and sales proposal software to internal communication tools. Before you commit to a provider, make a complete list of the applications your team uses every day. Then, verify that the SSO solution you’re considering can integrate with all of them. This step is crucial for creating the smooth, uninterrupted user journey that makes SSO so valuable. If it doesn’t work with the tools your team loves, adoption will be a struggle.
Plan for Team Training and Adoption
A new tool is only as good as your team's ability to use it. Rolling out SSO isn't just a technical change; it's a change in your team's workflow. To make the transition easy, create a simple adoption plan. Let everyone know what’s happening, why it’s an improvement (less password hassle, better security), and when the change will take place. A short training session or a clear, one-page guide can make a world of difference. When your team understands how to use the new system and feels confident, you’re more likely to see the full productivity gains that SSO can offer.
Best Practices for Implementing SSO
Implementing SSO is more than just flipping a switch. To truly reap the benefits of streamlined access and tighter security, you need a thoughtful strategy. Putting a few best practices in place from the start will help you build a system that’s not only efficient but also resilient. Here’s what your team should focus on to get it right.
Create Strong Authentication Policies
Think of authentication policies as the rulebook for your SSO system. They define who gets access to what and under which conditions. A great SSO solution lets you automate these rules, for instance, by granting access to certain apps based on a person’s role or department. This saves your IT team a ton of manual work. You can set policies that require stronger verification, like multi-factor authentication (MFA), for sensitive applications while keeping it simple for everyday tools. Getting these policies right from the beginning is the key to a secure and smoothly running system.
Monitor and Audit Security Regularly
SSO makes logging in a breeze, but that convenience requires a bit of housekeeping. Regular security audits are non-negotiable. Think of them as a routine check-up to make sure everything is working as it should be. Audits help you confirm that access rights are up to date, which is especially important when team members change roles or leave the company. They also give you a chance to spot any unusual login patterns that could signal a problem. By regularly reviewing access logs and permissions, you ensure your security policies are being followed and your company’s data stays protected.
Prioritize Employee Security Training
Your team is your first line of defense, so getting them up to speed on security is essential. SSO simplifies their workday, but it also concentrates access into a single credential, making that one password incredibly important. Your training should cover the basics of good security hygiene: how to create a strong password, why they should never share it, and how to spot phishing attempts that might try to steal their login information. When your employees understand the "why" behind the security measures, they become active participants in protecting the company. This kind of security awareness training is a crucial piece of the puzzle.
Have a Backup Access Plan
What happens if your SSO provider has an outage? It’s a question you need to answer before it happens. If your SSO system goes down, your team could be locked out of every application they need to do their jobs, effectively grinding work to a halt. That’s why having a backup access plan is so important. This could involve having alternative, direct login methods for critical systems or a clear communication plan to keep everyone informed during an outage. A solid disaster recovery plan ensures that a single point of failure doesn’t bring down your entire operation.
Related Articles
- 10 Common Security Questions & Answers: Best Practices | Iris AI
- Iris Blog - Win More Deals with Security Questionnaires
Frequently Asked Questions
Is having just one password for everything actually secure? It’s a fair question, but yes, it can be much more secure. The strength of SSO comes from encouraging everyone to create one incredibly strong, unique password instead of juggling multiple simple ones. When people only have to remember a single password, they’re more likely to make it complex. The real security power-up, however, comes from pairing SSO with multi-factor authentication (MFA). This combination means that even if someone managed to get the password, they still couldn't get in without a second verification step, like a code from a phone.
How is SSO different from using a password manager or my browser's autofill? While they might feel similar from your end, they work very differently behind the scenes. A password manager is a personal tool that stores your individual login credentials for various sites and helps you fill them in. SSO, on the other hand, is an authentication system managed by your company. It doesn't just store your passwords; it creates a trusted connection that logs you into applications automatically after you verify your identity once. This gives your company centralized control over access and security, which is something a personal password manager can't do.
We use a lot of different apps. Will SSO work with all of them? This is one of the most important things to check before you get started. Most modern, cloud-based applications are built to work with SSO using standard protocols like SAML or OpenID Connect. However, older or custom-built software might not be compatible. The best first step is to make a list of every application your team absolutely needs for their daily work. Then, when you evaluate SSO providers, you can confirm that they can integrate with your entire software stack.
You mentioned SSO and MFA work together. Do we really need both? Think of it this way: SSO is like having a master key to every door in your office, which is incredibly convenient. MFA is the security guard at the front door who checks your ID before letting you in. Using SSO alone gives you convenience, but it also creates a single entry point that needs extra protection. By adding MFA, you secure that entry point, ensuring that only the right people can use that master key. They truly are better together for a secure and efficient system.
What's the biggest challenge when a company starts using SSO? Honestly, the technology itself is usually pretty straightforward. The biggest challenge is often the human side of the change. A successful rollout depends on clear communication and team adoption. You need to explain to everyone what is happening, why it's an improvement for them (less password hassle!), and how to use the new system. A little bit of planning for training and support goes a long way in making the transition smooth for the entire team.
Share this post
Link copied!












_EasiestToDoBusinessWith_EaseOfDoingBusinessWith.svg)
_HighPerformer_HighPerformer.svg)





_BestSupport_QualityOfSupport.svg)